TL;DR, most of the security news about IoT is full of FUD. Always put the risks in context - who can exploit this and what can the attacker do with it. Most story only covers the latter.
Introduction
There is rarely a day without news that another "Internet of Things" got hacked. "Smart" safes, "smart" rifles, "smart" cars, "smart" fridges, "smart" TVs, "smart" alarm systems, "smart" meters, "smart" bulbs, NAS devices, routers. These devices are getting hacked every day. Because most of these devices were never designed with security as a goal, and some of them have been never tested by security professionals, it is no surprise that these things are full of vulnerabilities.
Independent security researchers find these vulnerabilities, write a cool blog post or give a presentation about the vulnerability and the exploit, and the media forgets the constraints just for the sake of more clicks. "We are all doomed" we can read in the news, but sometimes the risks are buried deeply in technical jargon. Please note I blame the news sites here, not the researchers.
 |
| http://www.slideshare.net/danielmiessler/iot-attack-surfaces-defcon-2015 |
There are huge differences between the following risks:
- Attackers can directly communicate with the router (or camera) from the Internet without authentication and exploit the vulnerability. This is the worst-case scenario. For example, an automated ransomware attack against your NAS is pretty bad.
- Attackers have to position themselves in the same WAN network (e.g. Sprint mobile network in the case of Jeep hacking) to exploit the vulnerability. This is still pretty bad.
- The vulnerable code can not be triggered directly from the Internet, but tricks like CSRF can be used to exploit it (details later in this post).
- The vulnerable code can not be triggered directly from the Internet, and it uses a protocol/port which prevents Cross Protocol Scripting. Attackers have to access the local network before exploiting this vulnerability.
Network exposure
Most devices are behind an IPv4 NAT device (e.g. home router), thus can not be reached from the Internet side by default. Except when the device configures the firewall via UPNP. Or the device has a persistence cloud connection, and the cloud can send commands to the device. Or the device uses IPv6 tunneling (e.g. Teredo), thus it is reachable from the Internet. But not every vulnerability on your home network is accessible directly from the Internet. As more and more devices and networks will support IPv6, this scenario might change, but I hope most home routers will come with a default deny configuration in their IPv6 firewall module. On the other hand, scanning for IPv6 devices blindly is not feasible due to the large number of IPv6 addresses, but
some tricks might work.
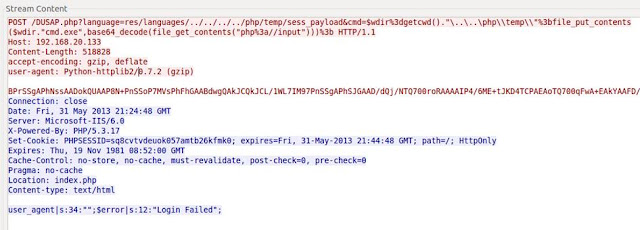
If attackers can not access the device directly, there is a way to hack it through the user's browser. Just convince the victim user to visit a website, and via
CSRF (Cross Site Request Forgery) and brute-forcing the device IP, it is possible to hack some devices (mostly through HTTP - if the exploit can fit into simple GET or POST commands.
If attackers can not attack the device vulnerability through the Internet directly, or via CSRF, but have connected to the same network - the network exposure shrinks significantly. And when attackers are on the same network as you, I bet you have bigger problems than the security of the IoT devices ...
Recommendations for home users
Don't buy **** you don't need
Disconnect from the power cord the IoT devices you don't need to operate 7*24.
Disable cloud connectivity if it is not necessary. For example, I have a NAS device that can be reached through the "cloud", but I have disabled it by not configuring any default gateway for the device. I prefer connecting to my network via VPN and reach all my stuff through that.
Prevent CSRF attacks. I use two tricks. Don't use the 192.168.0.x - 192.168.10.x network at-home - use an uncommon IP range instead (e.g. 192.168.156.x is better). The second trick is I configured my Adblock plugin in my primary browser to block access to my internal network. And I use another browser whenever I want to access my internal devices. Update: On Firefox you can use NoScript ABE to block access to internal resources.
Check your router configuration:
- disable UPnP
- check the firewall settings and disable unnecessary port forwards
- check for IPv6 settings, and configure the firewall as default deny for incoming IPv6 TCP/UDP.
Run Nmap to locate new IoT in your home network :)
Run a WiFi scan to locate new WiFi access points. Let me share a personal experience with you. I moved to a new house and brought my own WiFi router with me. I plugged it in, and forget about WiFi. Months later it turned out I had two other WiFi devices in my house - the cable modem had its own integrated WiFi with default passwords printed on the bottom, and the Set-top-box was the same - default WiFi passwords printed on the bottom. And don't forget to scan for ZigBee, Bluetooth, IrDA, FM, ...
Update your devices - in case you have a lot of free time in your hand.
Don't allow your guests to connect to your home network. Set up a separated AP for them. Imagine your nephew stealing your private photos or videos from your NAS or DNLA server.
With great power, comes great responsibility. The less device you own in your house, the less time you need to maintain those.
Read the manuals of your devices. Be aware of the different interfaces. Configure it in a secure way.
Disable Teredo protocol in case you don't need IPv6.
Update: Prevent against DNS rebind attacks via configuring a DNS server which can block internal IP addresses. OpenDNS can block internal IP, but this is not a default option, you have to configure it.
Recommendations for vendors
For vendors, I recommend at least the followings:
- Implement security during Software Development LifeCycle
- Continuous security testing and bug bounties
- Seamless auto-update
- Opt-in cloud connectivity
Recommendations for journalists
The questions to ask before losing your head
- who can exploit the vulnerability?
- what prerequisites do we have about the attack to successfully exploit the vulnerability? Is the attacker already in your home network? If yes, you have probably bigger problems.
- what can the attacker do when the exploit is successful?
And last but not least, don't forget that in the case of IoT devices, sometimes users are the product, not the customer. IoT is about collecting data for marketing purposes.
Related word
- El Hacker
- Rom Hacking
- Hacking Course
- Hacking Wireless 101 Pdf
- Mind Hacking
- Growth Hacking Tools
- Javascript Hacking
- Etica Hacker
- Hacking Academy
- Javascript Hacking
- Curso Ethical Hacking